Steps Wifi Hacking Cracking WPA2 Password After the long holiday, first I want to say Merry Christmas and Happy new year 2. Today we will learn about 5 Steps Wifi Hacking Cracking WPA2 Password. A lot of readers send many request regarding how to crack wireless WPA2 password in our request tutorial page. According to Wikipedia Wi Fi Protected Access WPA and Wi Fi Protected Access II WPA2 are two security protocols and security certification programs developed by the Wi Fi Alliance to secure wireless computer networks. The Alliance defined these in response to serious weaknesses researchers had found in the previous system, WEP Wired Equivalent Privacy A flaw in a feature added to Wi Fi, called Wi Fi Protected Setup WPS, allows WPA and WPA2 security to be bypassed and effectively broken in many situations. Many access point they have a Wifi Protected Setup enabled by default even after we hard reset the access point. Requirements 1. Wireless card support promiscuous mode In this tutorial I use ALFA AWUS0. Today we will learn about 5 Steps Wifi Hacking Cracking WPA2 Password. A lot of readers send many request regarding how to crack wireless WPA2 password in our. H from Amazon. 2. Access point with WPA2 and WPS enables 5 Steps Wifi Hacking Cracking WPA2 Password 1. Open our terminal CTRLALTT and type airmon ng view tips and tricks how to create keyboard shortcut on kali linux this command will lists our wireless card that attached with our system. How-to-install-VirtualBox-Guest-Additions-in-Kali-Linux-blacKMORE-Ops.png' alt='How To Install Usb Wifi Adapter On Kali Linux Vmware' title='How To Install Usb Wifi Adapter On Kali Linux Vmware' />The next step we need to stop our wireless monitor mode by running airmon ng stop wlan. Human Body Pushing The Limits Rapidshare. Now we ready to capture the wireless traffic around us. By running airodump ng wlan. From the picture above, we can see many available access point with all the information. In the green box is our victim access point which is my own access point Information BSSID Basic Service Set Identification the MAC address of access point. PWR Signal level reported by the card. Beacons Number of announcements packets sent by the APData Number of captured data packets if WEP, unique IV count, including data broadcast packets. Number of data packets per second measure over the last 1. CH Channel number taken from beacon packets. MB Maximum speed supported by the AP. This stepbystep article shows you how to install Kali Linux 2. VMware Workstation stepbystep but you can also use VMware Player which is free. This tutorial. 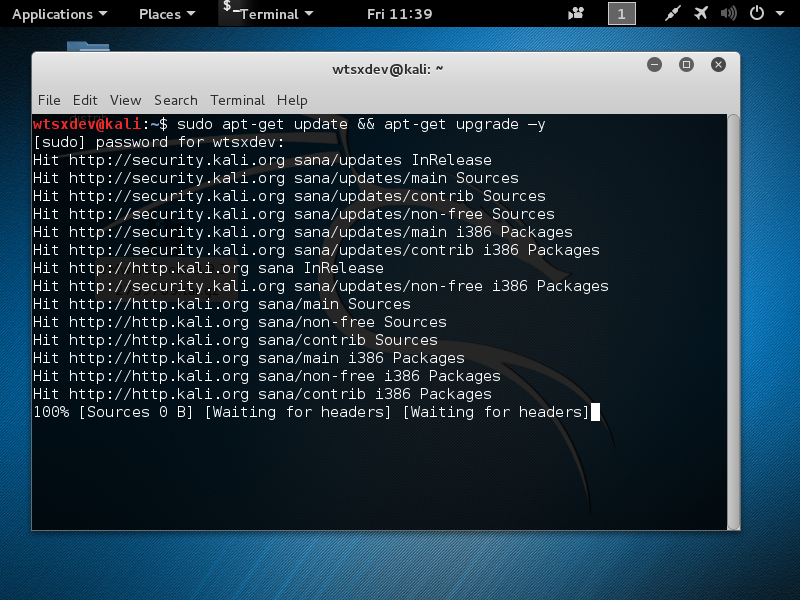 If MB 1. MB 2. 2 its 8. ENC Encryption algorithm in use. CIPHER The cipher detected. TKIP is typically used with WPA and CCMP is typically used with WPA2. AUTH The authentication protocol used. ESSID Shows the wireless network name. The so called SSID, which can be empty if SSID hiding is activated. From the step 3 above, we can find access point with encryption algorithm WPA2 and note the AP channel number. Now we will find out whether target AP has WPS enabled or not. C s if the WPS Locked status is No, then we ready to crack and move to step 5. The last step is cracking the WPA2 password using reaver. MAC address fail wait3. Because we already get the information from step 3 above, so my command look like this reaver i wlan. E0 0. 5 C5 5. A 2. WPA2 password vishnuvalentino. Kali virtual. Box, but it depend with our hardware and wireless card. Conclusions 1. WPA and WPA2 security implemented without using the Wi Fi Protected Setup WPS feature are unaffected by the security vulnerability. To prevent this attack, just turn off our WPSQSS feature on our access point. See picture below I only have the Chinese version Notes Only practice this tutorial on your own lab and your own device. Hacking can be a crime if you dont know where to put it. Share this article if you found this post was useful.
If MB 1. MB 2. 2 its 8. ENC Encryption algorithm in use. CIPHER The cipher detected. TKIP is typically used with WPA and CCMP is typically used with WPA2. AUTH The authentication protocol used. ESSID Shows the wireless network name. The so called SSID, which can be empty if SSID hiding is activated. From the step 3 above, we can find access point with encryption algorithm WPA2 and note the AP channel number. Now we will find out whether target AP has WPS enabled or not. C s if the WPS Locked status is No, then we ready to crack and move to step 5. The last step is cracking the WPA2 password using reaver. MAC address fail wait3. Because we already get the information from step 3 above, so my command look like this reaver i wlan. E0 0. 5 C5 5. A 2. WPA2 password vishnuvalentino. Kali virtual. Box, but it depend with our hardware and wireless card. Conclusions 1. WPA and WPA2 security implemented without using the Wi Fi Protected Setup WPS feature are unaffected by the security vulnerability. To prevent this attack, just turn off our WPSQSS feature on our access point. See picture below I only have the Chinese version Notes Only practice this tutorial on your own lab and your own device. Hacking can be a crime if you dont know where to put it. Share this article if you found this post was useful.